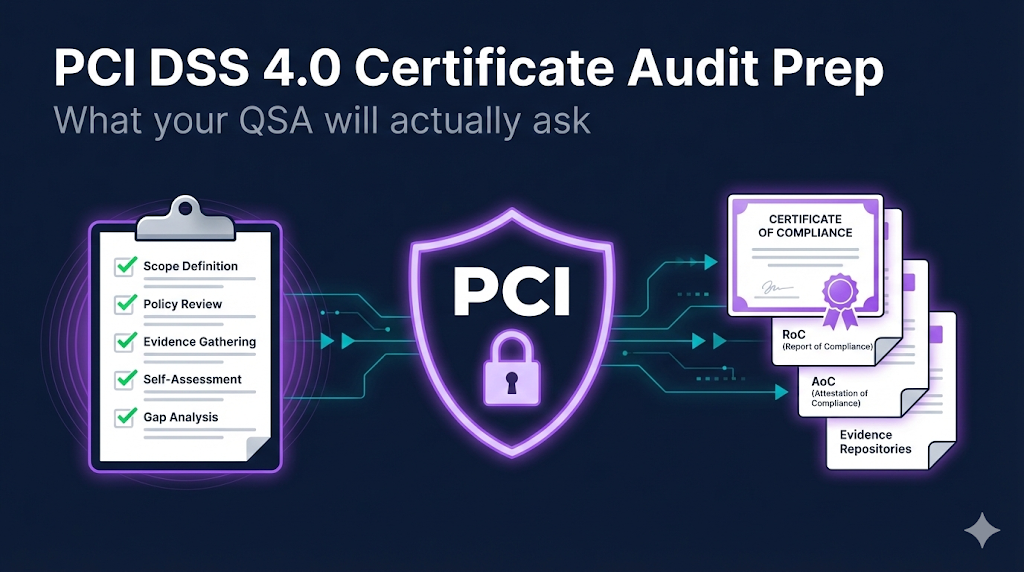
PCI DSS 4.0 Certificate Audit Prep
Everything your QSA will ask about certificates and encryption. PCI DSS 4.0 has 12 requirements—this checklist focuses on Requirement 4 (protect cardholder data in transit) and related certificate controls.
When to Use
- • Preparing for PCI DSS 4.0 assessments
- • Gathering evidence for QSA interviews
- • Fixing certificate-related findings before the audit
- • Training security teams on PCI crypto requirements
Do NOT Use For
- • SAQ A merchants with no CHD handling (outsourced everything)
- • Systems outside the cardholder data environment (CDE)
Quick Reference (TL;DR)
- TLS 1.2 minimum, TLS 1.3 recommended—no legacy protocols
- Forward secrecy required (ECDHE/DHE ciphers)
- No weak ciphers: NULL, RC4, 3DES, export ciphers
- No self-signed certs on public endpoints; complete chain required
- Document your certificate inventory (Requirement 12.3.3 is new)
- Know your scope before anything else
11. Know Your Scope
Objective: Document what systems are in scope before anything else—this is the QSA's first question
💡 **This is the QSA's first question.** If you can't define scope, everything else is harder.
💡 Internal TLS connections are often forgotten—don't overlook service mesh and database links.
💡 QSAs will ask how you govern third-party TLS termination—have their AOCs and crypto configs ready.
22. Requirement 4.2.1 - Protocol Requirements
Objective: "Strong cryptography is used to safeguard PAN during transmission over open, public networks"
Test protocol support:
# Should succeed
openssl s_client -connect payment.example.com:443 -tls1_2 2>&1 | head -5
# Should fail (TLS 1.0 disabled)
openssl s_client -connect payment.example.com:443 -tls1 2>&1 | head -5💡 **Common finding:** TLS 1.0 or 1.1 still enabled on legacy systems.
💡 Prepare server config exports and SSL Labs reports as evidence.
33. Requirement 4.2.1 - Cipher Suite Requirements
Objective: Verify cipher configuration meets PCI DSS 4.0 standards
Export cipher list from server:
nmap --script ssl-enum-ciphers -p 443 payment.example.com💡 **New in 4.0:** Forward secrecy is now explicitly required, not just recommended. Be prepared to show at least one config/export demonstrating ECDHE in use.
💡 3DES removal is new—many legacy systems still have it enabled.
💡 💡 Document which cipher policy baseline you follow (e.g., NIST SP 800-52r2) and keep that doc handy as evidence.
44. Key Strength Requirements
Objective: Ensure certificate keys meet minimum strength thresholds
Check key size:
openssl x509 -noout -text -in cert.crt | grep "Public-Key"Generate 2048-bit DH parameters:
openssl dhparam -out dhparam.pem 2048💡 DH parameters are the most commonly overlooked—many servers use 1024-bit defaults.
💡 **Retire any 1024-bit keys within scope**, even if not internet-facing. QSAs scrutinize internal services too.
💡 Document certificate details as evidence.
55. Certificate Lifecycle Controls
Objective: Be ready for QSA questions about how you manage certificates
💡 QSAs want to see process, not just technology. Document your runbooks.
💡 **Pro tip:** Have specific people assigned to answer each area. QSAs notice when everyone looks at each other.
66. Evidence Collection Checklist
Objective: Gather these BEFORE the QSA arrives
💡 Organize evidence in a shared folder or binder before the audit.
💡 Some QSAs still want paper copies—be prepared.
77. Common Findings & Fixes
Objective: Fix these before the QSA arrives
💡 **Fix critical findings first**—these will fail the audit.
💡 Medium findings won't fail you but show gaps in security posture.
88. Requirement Mapping Quick Reference
Objective: Understand which PCI requirements map to certificate/crypto controls
💡 **New in 4.0:** Requirement 12.3.3 explicitly requires organizations to maintain a cryptographic inventory. Certificates are a key part of this.
💡 This checklist focuses on Requirement 4, but key management (Req 3) is equally important. See our key ceremony best practices for what auditors look for in key generation procedures.
99. 30-Day Audit Prep Timeline
Objective: Systematic preparation beats last-minute scrambling
💡 Start early—30 days is minimum for thorough preparation.
💡 If you find issues, you need time to fix them AND verify the fixes.
Troubleshooting
Problem: QSA asks for cryptographic inventory and we don't have one
Solution: Start with certificate inventory from your CLM tool. Document all TLS endpoints, algorithms in use, and key storage locations. This is now required under Requirement 12.3.3.
Problem: Legacy system requires TLS 1.0 for compatibility
Solution: Document a compensating control: network segmentation, enhanced monitoring, planned upgrade timeline. Use the PCI Council's standard Compensating Control Worksheet—QSAs expect to see it in that format.
Problem: Can't disable 3DES due to legacy integrations
Solution: Similar to TLS 1.0: document the business justification, implement compensating controls, and show a migration plan. 3DES removal is new in 4.0, so QSAs are seeing this frequently.
Problem: Certificate expired during previous assessment period
Solution: Be honest. Show what monitoring you've implemented to prevent recurrence. QSAs respect transparency and demonstrated improvement over cover-ups.
Problem: Private keys stored on application servers without HSM
Solution: This isn't automatically a failure, but document your controls: file permissions, encryption at rest, access logging. HSMs are best practice but not always required.